Phishing Trends Report 2026
The 2026 Phishing Trends Report is the industry’s leading benchmark for phishing attacks that bypass security filters and trigger malicious clicks. Over 50 million data points were collected from the real and simulated threat reports of over 4 million Hoxhunt users from around the world.
Connecting phishing simulation results to real threat detection outcomes unlocks new dimensions of analysis, insight, and interventions. These stats and trends help security awareness leaders deliver risk-relevant training, while CISOs can prioritize defensive measures against the top emerging threats.
This report includes new findings on AI-generated phishing attacks and the latest malicious attachments, recruitment and calendar scams, and so much more. It helps paint a clearer picture of evolving trends in the phishing landscape and its effect on human cyber behavior.
Key Takeaways
AI generated phishing campaign surge
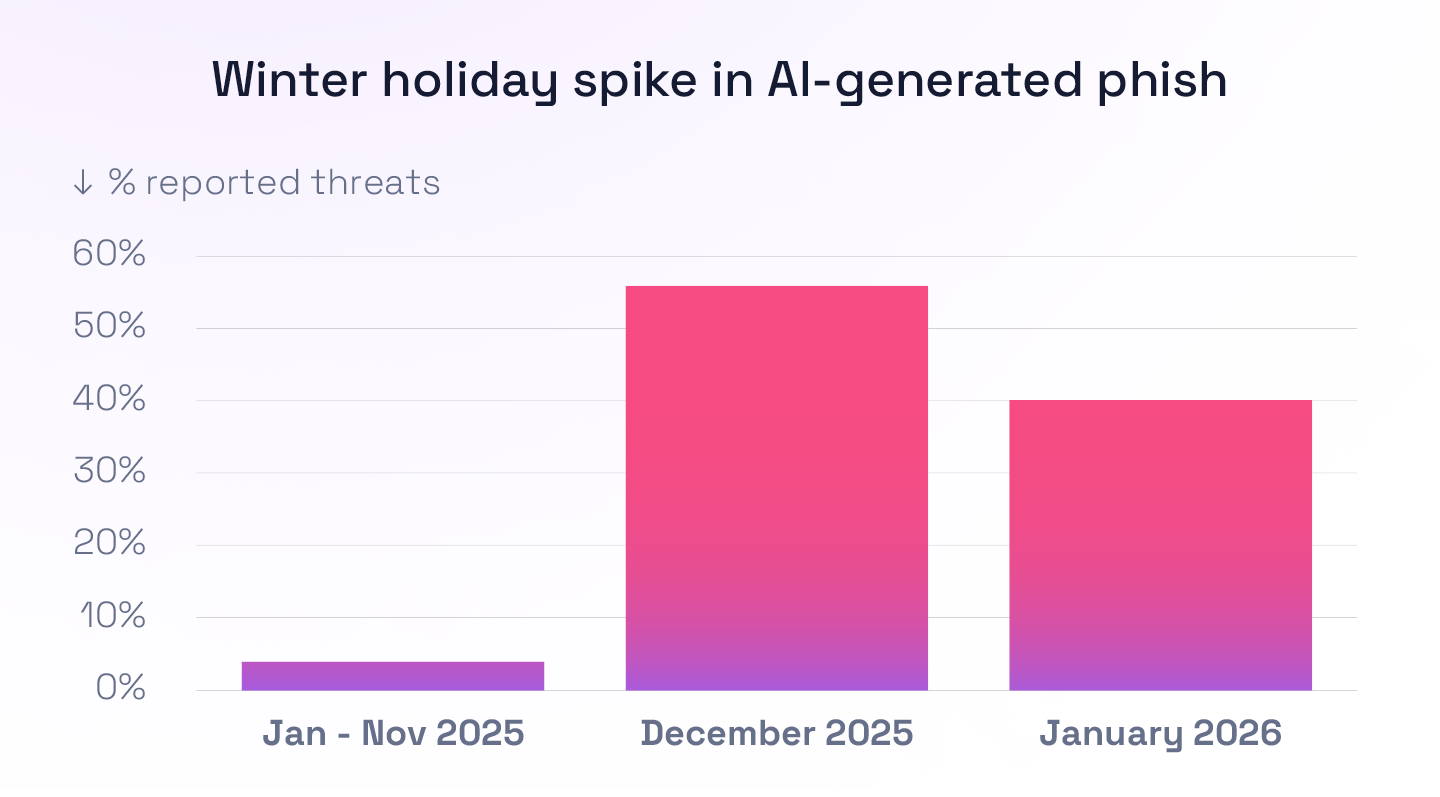
- 14x December increase in AI-generated phishing emails that bypasses email security filters
- After holding steady 1%-4% of all reported threats AI-generated phishing emails surged to 56% in December 2025 and dipped to 40% in January 2026
- 43% of AI phishing emails use malicious links
Callback, maybe: Rise of callback phishing
- 500% increase in callback phishing campaigns in 2025 (VIPRE Security)
- 27% of all callback phishing emails were financial service impersonations (Hoxhunt)
- 27% were classified as invoice-themed (Hoxhunt
Performance by region, phishing theme, industry, and job role
- Regional performance: The United States’ rate of successfully recognizing and reporting a phishing attack is significantly lower than high-performing European countries like Finland, Germany, and Switzerland.
- Industry performance: Financial Services is the highest performing sector, while Healthcare is particularly challenged.
- Job role performance: Communications has a 40% poorer phishing simulation failure rate than top-performing Finance.
- Phishing theme performance: Spoofed inter-org communications, like HR or IT notifications, are the most-clicked phishing simulations at 7.4% failure rate, followed by invoice scams.
Download the full report to see the full set of performance benchmarks along with expert insights.




