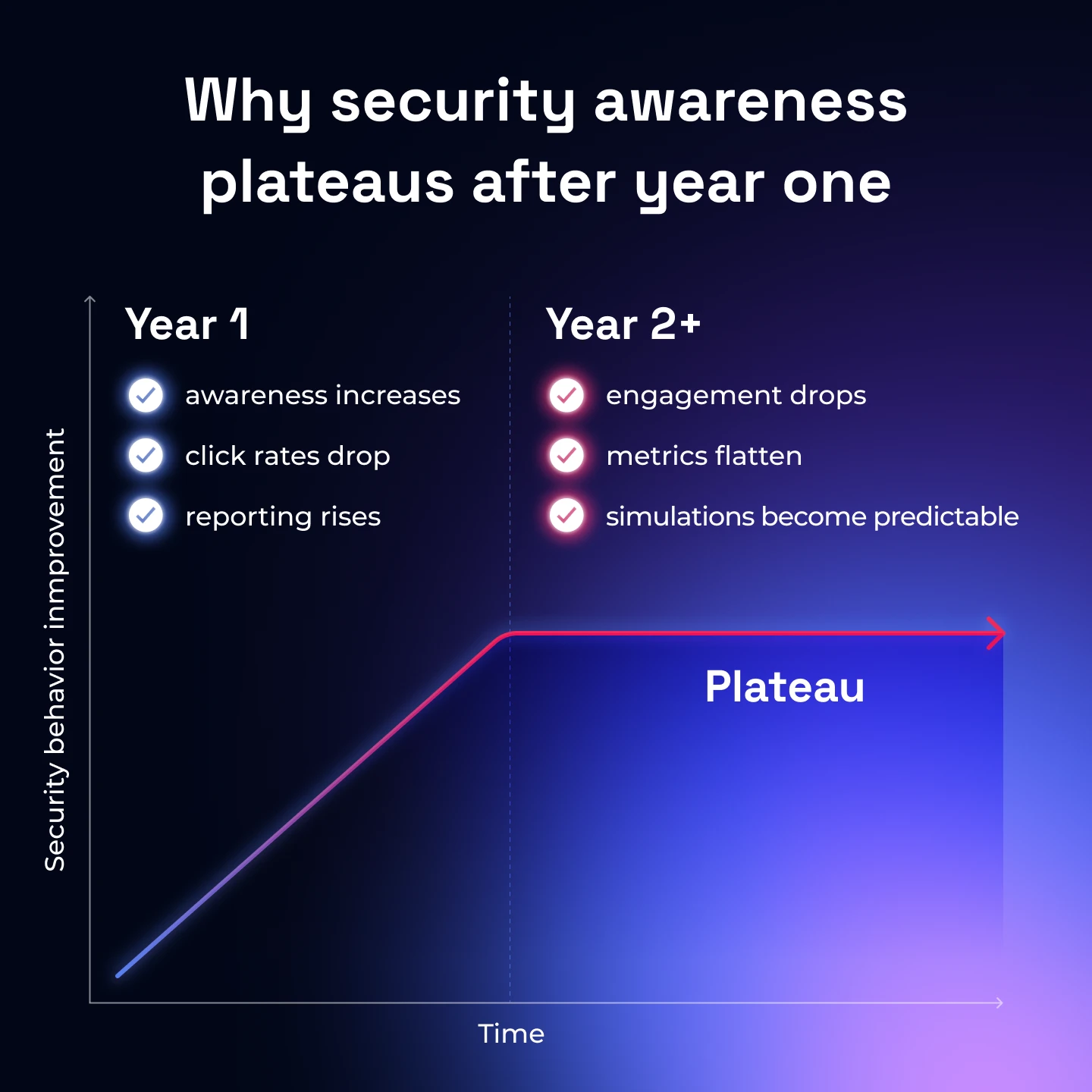
Security awareness programs often show their biggest improvements in the first year.
Click rates drop and leadership sees visible progress, but at some point the metrics stop improving. Engagement starts to fade, phishing simulations become predictable and the same behaviors begin repeating quarter after quarter.
This is the point where many awareness teams realize the program has plateaued. Not because security awareness doesn’t work, but because most programs are designed to drive initial improvement, not continuous behavior change.
Below we’ll break down why security awareness training often stalls after the first year, the structural mistakes that cause it and what mature programs do differently to keep improving employee security behavior over time.
How to tell when your security awareness program has plateaued
Most plateaus don’t happen suddenly, they show up gradually in the metrics.
In the first year of a security awareness rollout, improvements are usually easy to see. Click rates drop quickly, reporting increases, and employees begin recognizing obvious phishing attempts.
But after that initial progress, metrics stop moving and feel flat. That could be failure rates, reporting rates or overall engagement with training.
At this stage, the program may still appear healthy on the surface and completion rates may still look strong… but underneath those activity metrics, behavior change has slowed or stopped.
Common signs a program has plateaued include:
- Failure rates that stop improving after an initial drop
- Reporting rates that flatten instead of continuing to rise
- Training engagement declining after the initial rollout
- The same users repeatedly failing simulations
- Employees recognizing simulations rather than threats
When these patterns appear together, the issue usually isn’t a lack of effort from the awareness team. It’s a structural limitation of the program design.
Most traditional awareness programs are optimized to drive early improvement, not long-term behavior change. Once employees learn the basics, the program often stops challenging them and progress naturally slows.
Why engagement drops after the initial rollout
Security awareness programs often launch with strong momentum.
The first year usually includes a major rollout: new training, new phishing simulations, internal communication campaigns, and leadership support. Employees are exposed to the topic more than they have been before, and engagement tends to be high.
Once the rollout phase passes, many programs shift into a more routine pattern. This generally looks like periodic training modules, scheduled phishing simulations and occasional reminders from the security team. And so over time, the experience begins to feel repetitive.
Part of the problem is that traditional awareness programs are designed around information delivery, not sustained behavior change. They assume that once employees have learned the basics, repeating the same material will reinforce the lesson.
In reality, people disengage quickly when content feels predictable or irrelevant to their daily work.
This is why many awareness teams notice a familiar pattern after the first year:
- Training completion becomes harder to maintain
- Employees pay less attention to simulations
- Participation in optional learning drops
- Security messaging starts blending into background noise
At this point, the issue isn’t that employees don’t care about security. It’s that the program has stopped giving them new challenges or new reasons to engage.
Without variation, realism, or increasing difficulty, even well-designed programs eventually lose their ability to hold attention.
Phishing simulations stop working when they become predictable
Phishing simulations are one of the most effective tools in security awareness. Early in a program, simulations expose employees to threats they may never have encountered before. Users learn to slow down, examine messages more carefully, and recognize common phishing signals.
That’s why failure rates often drop quickly in the first year.
But over time, employees begin recognizing the simulation itself, rather than analyzing the message like they would a real attack.
Once users learn the patterns, the exercise stops functioning as a realistic security test. Instead of asking “Is this a real attack?”, employees start asking “Is this another training email?” At that point the simulation is no longer reinforcing real-world detection skills, it’s testing whether employees can recognize the training system.
This is why many awareness teams see a frustrating pattern: phishing failure rates keep dropping, but real phishing incidents don’t decline at the same pace.The program is still producing metrics, but the simulations are no longer challenging employees in the same way real attackers do.
To keep their learning value, simulations need to evolve over time - becoming more varied, more realistic, and harder to predict.
Training fatigue: when awareness becomes background noise
Another reason awareness programs plateau is training fatigue. Many programs rely on the same pattern year after year: mandatory modules, periodic phishing tests, and occasional reminder emails from the security team.
At first this works well, employees are learning new concepts and encountering threats they haven’t seen before. But over time, the experience starts to feel repetitive.
Long training modules become something employees rush through to complete, simulations feel like another test to pass and security messages begin blending into the background of an already busy workday.
When training feels like a compliance exercise rather than something useful, engagement naturally drops.
Part of the issue is that traditional awareness training is designed around knowledge transfer, not habit formation. Employees may remember the key points immediately after completing training, but without regular reinforcement those lessons fade quickly. Months later, many of the details have already been forgotten.
This creates a cycle where the organization repeats the same awareness material each year in an attempt to maintain baseline knowledge. Unfortunately, repeating the same training rarely improves behavior once employees have already learned the basics.
That’s why many awareness teams eventually hear the same feedback from employees:
- “We’ve already done this training.”
- “It’s the same phishing examples every year.”
- “I know what phishing looks like.”
At that point the problem isn’t awareness, it’s engagement.
Without variation, shorter learning loops, or more relevant scenarios, even well-intentioned training eventually loses its ability to influence behavior.

Compliance-led training has a natural ceiling
Many security awareness programs start as a compliance requirement. Organizations need to demonstrate that employees have completed security training, acknowledged policies, and participated in periodic phishing simulations. As a result, programs are often designed around satisfying those requirements first.
In the early stages, this approach can still produce real improvements. Employees learn the basics of phishing, password hygiene, and safe data handling, and the organization establishes a baseline level of awareness.
But compliance programs are not designed to drive continuous improvement. Once employees complete the required training and understand the basic rules, the program has largely achieved its original objective. Repeating the same modules each year may reinforce knowledge, but it rarely leads to meaningful changes in behavior.
This is where many awareness teams encounter the plateau. Training completion remains high, simulations continue to run. and reports still show activity… but the behaviors that actually reduce risk (like detecting threats, reporting suspicious messages, and responding quickly) stop improving.
Part of the issue is that compliance metrics reward participation, not outcomes.
Programs often measure:
- Training completion rates
- Course scores
- Number of simulations sent
These metrics prove that training happened, but they don’t necessarily show whether employees are becoming better at detecting real attacks. Over time, the program becomes very good at maintaining compliance while making little additional progress in reducing human risk.
Breaking through this ceiling usually requires shifting the program’s focus from training completion to behavior change and measuring how employees actually respond to threats.
.webp)
Adaptive difficulty keeps employees learning
One reason awareness programs plateau is that the training stops evolving with the people taking it. In the early stages of a program, most employees are learning the basics around what phishing looks like, how attackers create urgency, and where to report suspicious messages. Simple simulations and introductory training work well at this stage because the concepts are new.
Once employees understand those fundamentals, repeating the same level of difficulty stops driving improvement. For more experienced users, simulations become too easy. They can quickly spot the obvious signals and move on without thinking much about the message.
For employees who still struggle, the opposite problem can happen. Simulations may feel confusing or frustrating, which reduces engagement and makes learning less effective.
When everyone receives the same training regardless of their skill level, progress eventually slows for both groups.
Adaptive difficulty solves this by adjusting the challenge level based on how employees actually perform.
For example:
- Employees who consistently report threats may start receiving more realistic simulations
- Users who struggle with certain scenarios may receive targeted micro-training
- Higher-risk roles can be tested with attacks that mirror what they actually encounter at work
This keeps the learning experience within the right level of challenge.
If training is too easy, employees become bored. If it’s too difficult, they disengage.
But when difficulty evolves alongside employee skill levels, the program can continue improving behavior well beyond the first year.
Realistic simulations matter more after year one
As employees gain training experience, obvious examples and simple simulations become less useful.
Real attackers rarely send emails filled with spelling errors or clearly suspicious domains. Modern phishing attacks are designed to blend into normal business communication. They often imitate internal workflows, vendor relationships, or everyday collaboration tools. (Below you can see some of the alarming patterns we uncovered in our 2026 Phishing Trends Report.)
This is why realism becomes far more important after the first year of a program. More realistic simulations challenge employees to analyze messages the way they would in real life.
For example, mature awareness programs increasingly simulate attacks such as:
- Vendor invoice requests or payment changes
- Executive impersonation messages
- HR or benefits notifications
- Document-sharing requests
- Internal collaboration messages through tools like Teams or Slack
These types of scenarios force employees to rely on judgment rather than pattern recognition.
Realistic simulations also introduce the psychological triggers attackers use - urgency, authority, curiosity, and familiarity. Learning to pause and question those signals is one of the most important habits security awareness programs try to build.
As programs mature, increasing realism helps maintain the learning curve. Employees are no longer just spotting obvious phishing cues, they’re practicing how to evaluate messages that look much closer to real attacks.

How mature awareness programs break the plateau
When awareness programs plateau, the problem is rarely that employees have stopped learning. More often, the program itself has stopped evolving.
Many traditional awareness initiatives operate as a training cycle: launch training, run phishing simulations, measure results, and repeat the process the following year. That model works well for establishing a baseline level of awareness but once employees understand the fundamentals, repeating the same cycle produces smaller and smaller improvements.
Mature programs approach the problem differently. Instead of running awareness as a periodic training activity, they treat it as an ongoing behavioral system that continuously develops employee detection skills.
In this model, the goal is not simply to reduce simulation failures. The goal is to strengthen the organization’s human detection capability over time.
That means focusing on signals such as:
- How often employees report suspicious messages
- How quickly threats are surfaced to the security team
- How consistently employees respond to unfamiliar situations
As these behaviors improve, employees begin functioning less like passive training recipients and more like an active detection layer within the organization.
This is the approach we use at Hoxhunt. Rather than running isolated training campaigns, the system continuously adapts simulations and micro-training based on how employees respond to threats. Each interaction (whether a click or a report) feeds back into the training environment, helping the program gradually strengthen employees’ ability to detect real attacks.
This continuous learning loop allows awareness programs to keep improving long after the first year of training, turning employees into a reliable early warning system for phishing and social engineering attacks.

The real goal of security awareness isn’t training, it’s behavior change
Security awareness programs are often judged by the activities they produce…
How many employees completed training, how many phishing simulations were sent, how much the click rate dropped during testing etc.
Those metrics show that a program is running, but they don’t always show whether human risk is actually decreasing. The real purpose of security awareness is to influence how employees behave when a suspicious message appears in their inbox.
- Do they pause before reacting?
- Do they question unexpected requests?
- Do they report the threat so the security team can investigate?
When awareness programs plateau, it’s usually because the focus remains on delivering training rather than strengthening those behaviors. Once employees understand the basics, progress depends on continuously reinforcing the habits that help them recognize and report threats.
That’s why the most effective programs eventually shift away from static training cycles and toward systems that help employees practice detection skills repeatedly over time.
When that happens, awareness stops being a yearly compliance exercise and becomes something far more valuable: a workforce that actively helps detect and surface attacks before they spread.
And when employees consistently notice and report suspicious activity, security awareness isn’t just running as a program anymore, it’s functioning as part of the organization’s defense system.
Security awareness questions leaders ask when results stop improving
- Subscribe to All Things Human Risk to get a monthly round up of our latest content
- Request a demo for a customized walkthrough of Hoxhunt






