What is human risk management software?
We can think of Human Risk Management (HRM) software as the missing operational layer between security awareness and real-world risk reduction. It doesn’t just teach employees what to do, it measures what they actually do, then intervenes.
At its core, HRM software combines:
- Behavioral analytics: tracking how users interact with threats (clicks, reports, ignores)
- Risk scoring: assigning measurable risk levels to individuals, teams, and roles
- Adaptive interventions: delivering personalized nudges, micro-training, or simulations
- Continuous feedback loops: improving behavior over time, not just once per year
This is a fundamental shift from legacy approaches.
What to look for in the human risk management software
The best Human Risk Management software helps you do more than deliver awareness training. It should measure user-level risk, adapt to behavior over time, and improve how employees detect, report, and respond to threats. The strongest platforms move beyond campaigns and support continuous human risk reduction across the business.
Many vendors now use Human Risk Management language, but not all platforms deliver the same depth. Some are still awareness-led tools with light risk features layered on top.
If a platform mainly measures completion rates and campaign performance, it is likely closer to traditional awareness training. Stronger HRM platforms continuously measure, adapt, and reinforce behavior at the individual level.
Some teams need phishing resilience fast. Others need risk visibility, stronger reporting behavior, or a broader operating model for reducing human risk over time. The right platform depends on the outcome you are trying to drive.
The most mature HRM approach is not just about awareness content or analytics dashboards. It connects user behavior, adaptive interventions, and real-world reporting into one continuous system.
Platforms that support adaptive training, measurable behavior change, and real threat reporting are better positioned for organizations that want to operationalize human risk—not just run awareness campaigns.
If your goal is broad awareness coverage, many established platforms can help. If your goal is to build a more mature Human Risk Management program with adaptive behavior change and stronger reporting outcomes, prioritize vendors designed for continuous risk reduction rather than campaign-based training alone.
HRM vs training-led security
Traditional security awareness programs assume that if users know better, they’ll act better.
HRM challenges that assumption. From what we see in security teams:
- Training completion ≠ secure behavior
- Phishing simulation results plateau after 6-12 months
- Users often don’t know where or how to report real threats
HRM software closes this gap by focusing on observable behavior, not theoretical knowledge.
What HRM software actually does
A modern HRM platform typically operates across three layers:
| Stage | What it does | Why it matters |
|---|---|---|
| Measure | Tracks user behavior such as phishing clicks, threat reports, ignored alerts, or other risky actions. | Moves the program beyond awareness metrics and shows what users actually do in real environments. |
| Model | Builds risk scores for individuals, teams, roles, or business units using behavioral signals and trend data. | Helps security teams prioritize higher-risk users and focus interventions where they can reduce the most risk. |
| Modify | Delivers personalized interventions such as adaptive phishing simulations, micro-training, or just-in-time nudges. | Turns insight into measurable behavior change instead of stopping at reporting or compliance completion. |
Key capabilities that define human risk management
Not all vendors labeled “HRM” actually meet this bar. At minimum, true HRM platforms include:
- Individual-level risk scoring (not just aggregate reporting)
- Adaptive phishing simulations (difficulty adjusts to user skill)
- Real threat reporting workflows (not just simulations)
- Behavior-triggered micro-training (just-in-time, not scheduled)
- Integration with email, identity, and SOC tools
This is where the category starts to separate and where many training platforms fall short.
How is human risk management different from security awareness training?
Security awareness training (SAT) is usually designed to educate. Human risk management is designed to reduce measurable risk.
Security teams are no longer just asking if employees completed, they’re asking tougher questions:
- Are users getting better at spotting real threats?
- Can we identify which people or teams create the most risk?
- Does the platform adapt based on behavior?
- Can we prove that human-layer risk is declining?
SAT focuses on knowledge and awareness, while HRM adds behavioral analytics, targeted interventions, and continuous monitoring to drive real behavior change.
The simplest difference: knowledge vs behavior
SAT assumes that once people know the rules, they will follow them.
HRM starts from a more realistic premise: people do not always act on what they know. They forget, rush, guess, click, misreport, and work around friction. So the job is not just to educate them once, it's to measure behavior continuously and improve it over time.
That is why HRM platforms tend to include:
- User-level behavioral signals
- Risk scoring
- Adaptive phishing or intervention logic
- Micro-training triggered by actions
- Threat reporting workflows
- Dashboards that show movement in risk, not just completion rates
| Category | Security Awareness Training (SAT) | Human Risk Management (HRM) |
|---|---|---|
| Primary goal | Teach employees about threats, policies, and compliance requirements. | Reduce measurable human-layer cyber risk through behavior change. |
| Core metric | Training completion rates, quiz scores, phishing click rates. | Behavior change, threat reporting quality, and risk reduction over time. |
| Intervention style | Scheduled courses, periodic campaigns, and broad phishing simulations. | Adaptive, personalized, and behavior-triggered interventions (micro-training, nudges). |
| User model | One-size-fits-all approach across the employee base. | Individual, team, and role-based risk segmentation with tailored experiences. |
| Time horizon | Campaign-based or annual training cycles. | Continuous monitoring, feedback, and improvement loops. |
| Operational value | Supports awareness and compliance reporting. | Provides actionable insights for security teams, SOC integration, and risk prioritization. |
The KPI problem: completion is easy, proof is hard
One reason this category is evolving so quickly is that old SAT metrics are increasingly weak buying signals. The problem is that SAT alone often cannot tell a credible risk-reduction story.
Completion rate is easy to report upward. It is much harder to prove that completion changed anything meaningful.
That is why HRM is gaining traction with security leaders who want stronger evidence:
- Did reporting rates improve?
- Did repeat-risk users improve faster with adaptive interventions?
- Did high-risk groups become easier to identify and coach?
- Did the SOC get more useful human-generated signals?
Which vendors are positioned as human risk management platforms?
The human risk management category is still evolving, which means vendor positioning is often ahead of actual capability.
Many platforms now use HRM language, but they fall across a spectrum:
- True HRM platforms (behavior + risk + intervention)
- Awareness-first platforms (training + phishing)
- Security platforms with HRM features layered in
Core vendors in the human risk management landscape
These vendors are frequently evaluated under the human risk category:
- Hoxhunt: Behavior-first HRM platform focused on adaptive training, real threat reporting, and measurable risk reduction
- CybSafe: Strong emphasis on behavioral science, analytics, and human risk scoring
- Mimecast Engage Awareness Training: Combines awareness training with behavioral signals and targeted interventions
- NINJIO: Focuses on engaging, story-driven training with personalization elements
| Vendor | Category fit | Why it qualifies as HRM |
|---|---|---|
| Hoxhunt | Strong HRM | Combines adaptive phishing simulations, personalized learning paths, real threat reporting, and behavior-change mechanisms designed to reduce measurable human risk over time. |
| CybSafe | Strong HRM | Centers its approach on behavioral science, human risk analytics, and user-level risk scoring—making it a strong fit for organizations prioritizing measurable human risk insight. |
| Mimecast Engage | Emerging HRM | Extends awareness training with behavioral signals, risk-based targeting, and more tailored interventions, though it remains closer to an awareness-led operating model than some dedicated HRM platforms. |
| NINJIO | Emerging HRM | Brings personalization and behavior-oriented training into the platform, but is still more training-centric than platforms built around continuous behavioral risk management from the ground up. |
Awareness-led platforms expanding into HRM
These vendors are not traditionally HRM but are increasingly adopting HRM positioning:
- KnowBe4: Market leader in security awareness training, now layering in risk scoring and adaptive elements
- Proofpoint Security Awareness: Combines phishing simulation and training with threat intelligence-driven personalization
- Guardey: Gamified awareness platform with lightweight behavioral features
| Vendor | Category fit | Positioning & limitations |
|---|---|---|
| KnowBe4 | SAT → HRM-adjacent | Strong training library and phishing simulations, but historically centered on campaign-based delivery and completion metrics rather than continuous behavioral risk modeling. |
| Proofpoint | SAT → HRM-adjacent | Deep threat intelligence and strong phishing capabilities, but HRM functionality is layered onto awareness workflows rather than built around continuous behavior change. |
| Guardey | SAT → Light HRM | Highly engaging, gamified training experience, but limited depth in behavioral analytics, risk scoring, and adaptive intervention at scale. |
Adjacent or emerging players
Some vendors are occasionally included in HRM conversations due to overlapping capabilities:
- Phished: Focused on phishing simulations and awareness
- Arctic Wolf: Integrates awareness into a broader managed security platform
- Huntress: Combines human coaching with managed detection and response
| Vendor | Category | Why it’s not full HRM |
|---|---|---|
| Phished | Awareness / Phishing Simulation | Primarily focused on phishing simulations and awareness training, without a full behavioral risk lifecycle or continuous risk scoring model. |
| Arctic Wolf | Managed Security Platform | Includes awareness capabilities within a broader managed security offering, but does not operate as a dedicated human risk management platform. |
| Huntress | MDR / Managed Detection & Response | Focused on threat detection and response with some human-layer support, but not built around continuous behavioral risk measurement and intervention. |
The key distinction buyers should use
Instead of relying on category labels, use this test:
Does the platform continuously measure behavior, assign risk, and adapt interventions at the individual level?
If yes → it’s likely true HRM
If no → it’s likely awareness-led or adjacent
Which platforms focus on phishing, identity, or broader human behavior?
Not all human risk management platforms are trying to solve the same problem.
Some are optimized for phishing defense, others for identity-related risk, and a smaller group focuses on holistic human behavior across multiple attack vectors.
Understanding this split helps you avoid a common mistake - buying a phishing platform when you actually need behavior change across the organization.
Phishing-focused platforms
These platforms are primarily designed to:
- Simulate phishing attacks
- Train users to detect suspicious emails
- Improve reporting rates
They are often:
- Highly effective at improving phishing resilience
- Easier to deploy quickly
- Familiar to most security teams
| Vendor | Focus | Strengths | Limitations |
|---|---|---|---|
| Proofpoint | Phishing + Threat Intelligence | Highly realistic phishing simulations informed by live threat intelligence, with strong alignment to email security ecosystems. | Less emphasis on broader human behavior beyond email-based threats and limited continuous behavior modeling. |
| KnowBe4 | Phishing + Awareness | Extensive phishing simulation library and scalable training programs suitable for large organizations. | Campaign-based approach can plateau over time, with limited adaptive behavior change mechanisms. |
| Phished | Phishing Simulation | Focused and specialized phishing detection training with straightforward deployment. | Narrow scope centered on phishing, with limited capability for broader human risk measurement or intervention. |
Best for:
- Organizations early in maturity
- Teams prioritizing phishing as the primary threat vector
Identity & behavior-signal-oriented platforms
These platforms move closer to HRM by:
- Incorporating user context
- Leveraging risk signals
- Adapting interventions based on behavior
| Vendor | Focus | Strengths | Limitations |
|---|---|---|---|
| Mimecast Engage | Email + Behavioral Signals | Uses behavioral signals and risk indicators to trigger targeted training and interventions aligned to user activity. | Still anchored to awareness workflows, with less depth in continuous behavioral modeling and risk scoring compared to full HRM platforms. |
| CybSafe | Behavioral Analytics | Strong focus on human risk scoring, behavioral data analysis, and identifying high-risk users across the organization. | Less emphasis on phishing simulation depth and real-time intervention workflows compared to phishing-first or full HRM platforms. |
Best for:
- Teams that want risk visibility + analytics
- Organizations moving beyond basic awareness
Broad human behavior platforms (full HRM scope)
These platforms treat human risk as a continuous, measurable system, not a set of campaigns.
They typically:
- Go beyond phishing into decision-making behavior
- Integrate with real threat reporting workflows
- Deliver adaptive, personalized interventions at scale
| Vendor | Focus | Strengths | Limitations |
|---|---|---|---|
| Hoxhunt | Phishing + Real Threat Reporting + Behavior Change | Combines adaptive phishing simulations, real threat reporting workflows, and personalized interventions to drive measurable behavior change and reduce human risk continuously. | Requires organizational alignment (process + culture) to fully leverage behavior-driven capabilities at scale. |
| NINJIO | Behavior + Engagement | Highly engaging, story-driven training with personalization that helps improve user awareness and behavior over time. | More training-centric, with less depth in continuous behavioral analytics and risk scoring compared to full HRM platforms. |
Best for:
- Enterprises prioritizing measurable human risk reduction
- Security teams integrating human signals into SOC workflows
The strategic trade-off
Each category reflects a different philosophy:
- Phishing-first platforms → optimize for detection of one attack vector
- Signal-driven platforms → optimize for visibility into human risk
- Full HRM platforms → optimize for continuous behavior change
The key is alignment. If your goal is to reduce phishing clicks, a simulation-heavy platform may be enough. If your goal is to reduce human-driven risk across the business, you need broader HRM capabilities.
How to choose the right focus
Choose phishing-focused if:
- Phishing is your dominant threat
- You need quick wins
Choose behavior-signal platforms if:
- You need visibility into risk
- You want to segment users and prioritize interventions
Choose full HRM platforms if:
- You need measurable risk reduction
- You want to operationalize human behavior as part of your security stack
Best human risk management software: vendor shortlist (2026)
Hoxhunt
Hoxhunt is built around a behavior-first model where employees become active threat detectors, not just trained users. The platform focuses on continuous behavior change and real-world signal generation.

Best for: Organizations prioritizing measurable human risk reduction and real threat reporting
Where it stands out:
- Real threat reporting as a core capability, not just simulations
- Adaptive phishing that evolves based on user skill and behavior
- High engagement via gamification and positive reinforcement
- Continuous learning model instead of scheduled campaigns
Where to pressure-test:
- Requires alignment with SOC workflows to fully unlock value
- Reporting and response processes need to be clearly defined internally
- Best results come when integrated into broader security operations
When this is the wrong choice:
- If your goal is purely compliance-driven awareness training
- If you’re not ready to operationalize human risk as part of detection
CybSafe
CybSafe approaches HRM from a behavioral science and analytics-first perspective, focusing on measuring and modeling human risk rather than primarily delivering training.

Best for: Security teams that want deep visibility into human risk and behavior patterns
Where it stands out:
- Strong human risk scoring and behavioral analytics
- Clear identification of high-risk users and groups
- Data-driven approach aligned with security metrics and reporting
Where to pressure-test:
- Less emphasis on phishing simulation depth compared to other platforms
- Intervention mechanisms may require pairing with training workflows
- Requires maturity to act on insights, not just observe them
When this is the wrong choice:
- If you want an out-of-the-box training-heavy solution
- If your team is not set up to act on behavioral insights
Mimecast Engage Awareness Training
Mimecast Engage extends a traditional awareness model with risk-based targeting and behavioral signals, especially within email-centric environments.
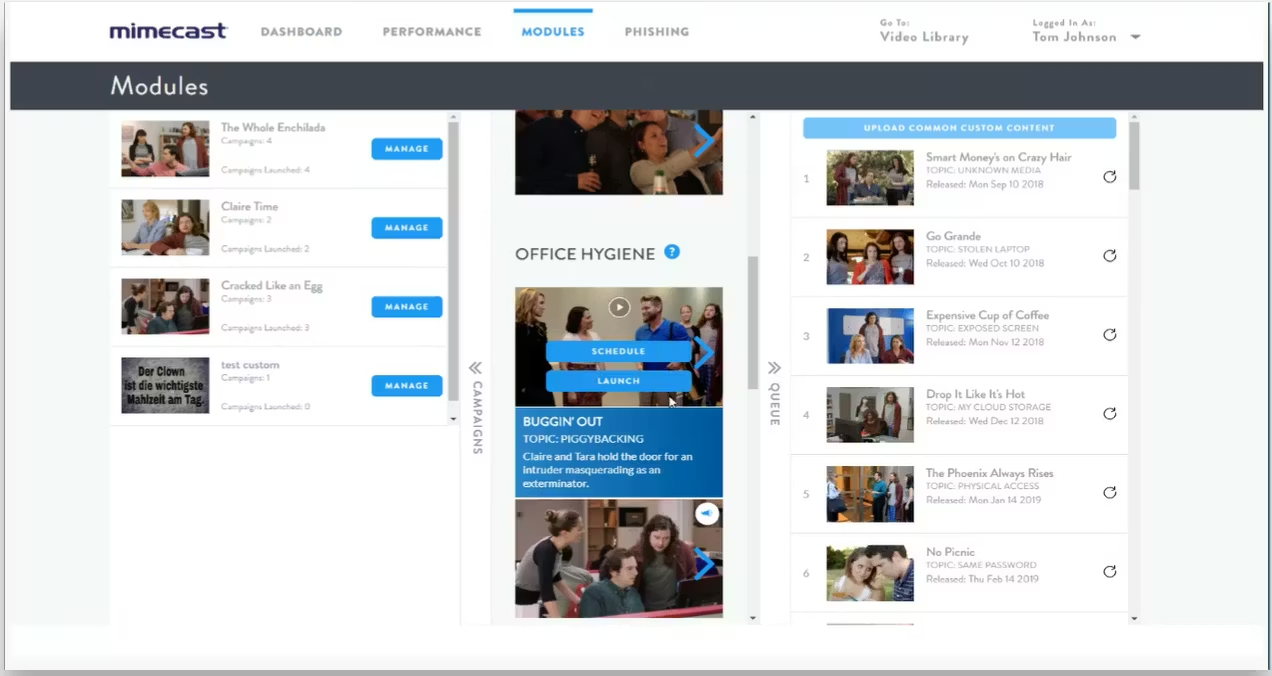
Best for: Organizations already invested in Mimecast looking to expand into HRM capabilities
Where it stands out:
- Tight integration with email security ecosystem
- Risk signals used to trigger targeted interventions
- Familiar model for teams transitioning from awareness platforms
Where to pressure-test:
- Still partially anchored in awareness-first architecture
- Behavioral modeling depth is more limited than dedicated HRM platforms
- Effectiveness depends on broader Mimecast ecosystem usage
When this is the wrong choice:
- If you want a standalone, behavior-first HRM platform
- If your security stack is not centered around Mimecast
NINJIO
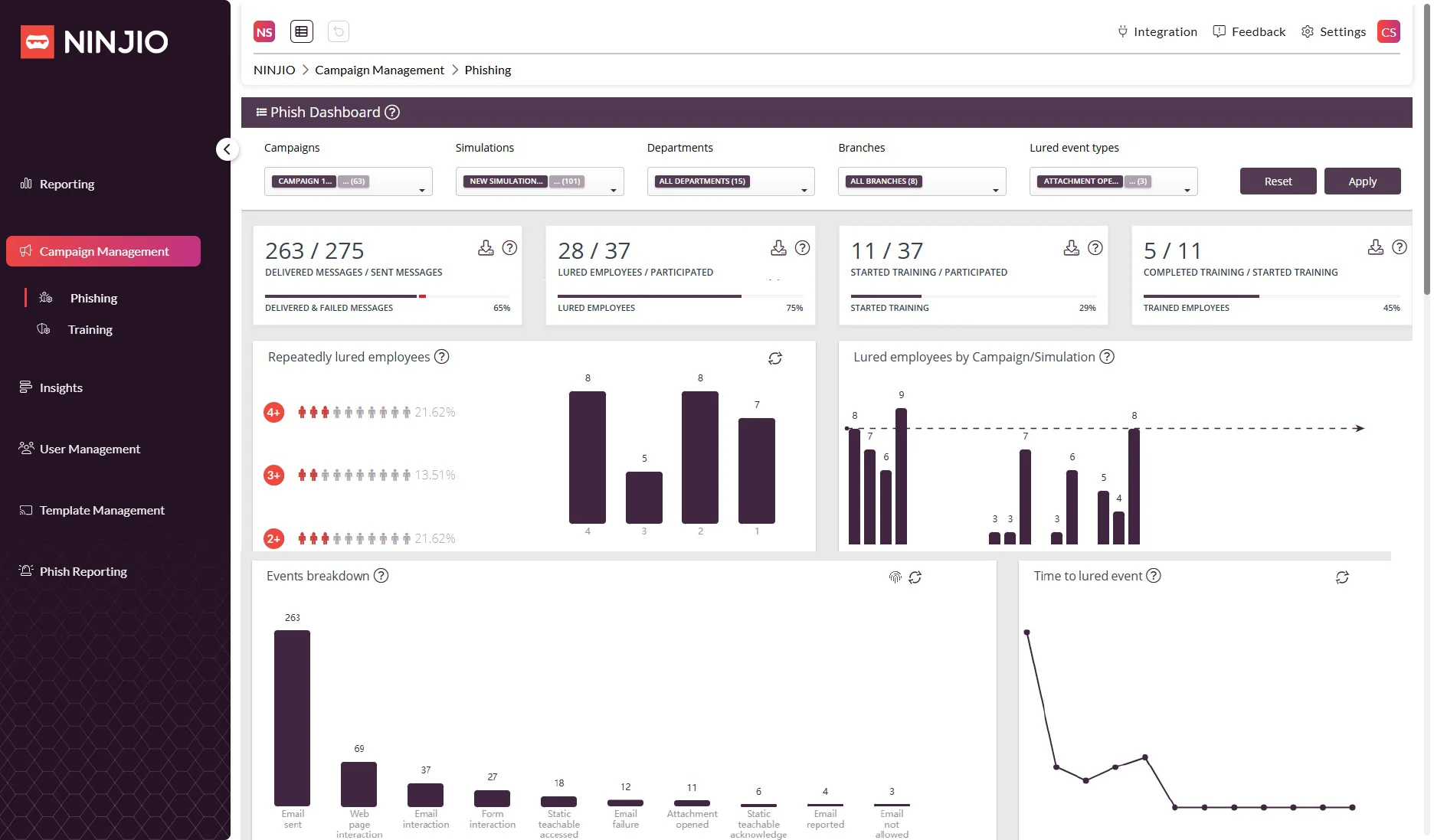
NINJIO focuses on engagement-led behavior change, using storytelling and media-driven training to drive awareness and retention.
Best for: Organizations prioritizing user engagement and security culture improvement
Where it stands out:
- Highly engaging, story-driven training format
- Strong adoption and completion rates across users
- Effective at improving baseline awareness and participation
Where to pressure-test:
- More training-centric than behavior-centric
- Limited depth in continuous risk scoring and adaptive interventions
- Less focus on real-time or behavior-triggered responses
When this is the wrong choice:
- If you need measurable, data-driven risk reduction
- If your priority is behavioral analytics and user-level risk scoring
KnowBe4
KnowBe4 is one of the most widely adopted platforms, built around scalable awareness training and phishing simulation at enterprise scale.
.webp)
Best for: Large organizations needing broad awareness coverage and compliance support
Where it stands out:
- Extensive content library and training breadth
- Mature platform with strong market adoption
- Scalable phishing simulation programs
Where to pressure-test:
- Often relies on campaign-based delivery rather than continuous adaptation
- Limited personalization compared to newer HRM platforms
- Harder to demonstrate measurable behavior change beyond training metrics
When this is the wrong choice:
- If your goal is continuous behavior change rather than awareness
- If you need adaptive, individualized training paths
Proofpoint Security Awareness
Proofpoint combines awareness training with real-world threat intelligence, focusing heavily on phishing realism and email-based attack defense.
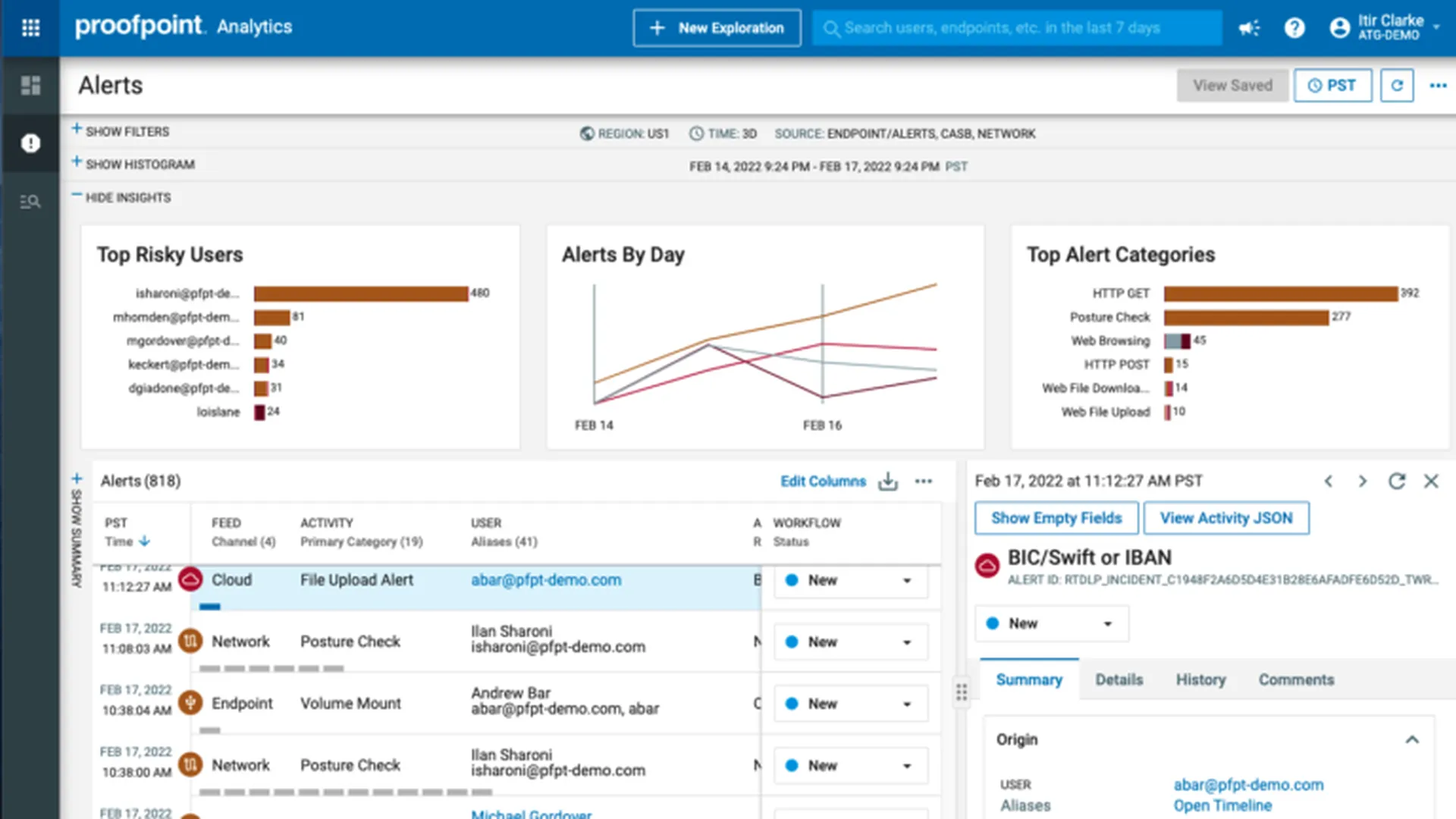
Best for: Organizations aligning awareness efforts closely with email security strategy
Where it stands out:
- Phishing simulations informed by real threat intelligence
- Strong alignment with email security workflows
- Effective for phishing-focused defense programs
Where to pressure-test:
- Heavily focused on email as the primary risk vector
- Less emphasis on broader human behavior across channels
- HRM capabilities are layered onto existing awareness models
When this is the wrong choice:
- If you want full-spectrum human risk management beyond phishing
- If your priority is behavior change across multiple attack surfaces
Comparison table: Best human risk management software
| Category fit | Strong HRM fit — built around continuous behavior change, adaptive interventions, and real threat reporting. |
|---|---|
| Core strength | Adaptive phishing, personalized training, and human-generated threat signals working together as one operating model. |
| Behavior change depth | High — per-user difficulty adjustment, ongoing reinforcement, and measurable improvement over time. |
| Reporting & operational value | Strong — combines user behavior data with real reporting workflows, helping security teams operationalize human risk rather than just track completion. |
| Best for | Organizations that want measurable human risk reduction, stronger reporting behavior, and a program that evolves with user maturity. |
| What to validate | How well the platform fits your SOC workflow, internal governance model, and appetite for a more behavior-driven program rather than a compliance-only rollout. |
| Category fit | Strong HRM fit — especially for teams that see human risk primarily as an analytics and measurement problem. |
| Core strength | Behavioral science, risk scoring, and visibility into human risk patterns across users and groups. |
| Behavior change depth | Medium-High — strong on measurement and modeling, though more insight-led than simulation-led. |
| Reporting & operational value | Strong — useful for teams that want human risk data to support prioritization, segmentation, and executive reporting. |
| Best for | Security teams prioritizing human risk visibility, analytics maturity, and clearer risk scoring across the workforce. |
| What to validate | Whether you need deeper phishing simulation realism or a more end-to-end intervention model alongside the analytics layer. |
| Category fit | Emerging HRM / awareness-led hybrid — strongest when used as an extension of Mimecast’s broader ecosystem. |
| Core strength | Risk-based interventions inside an email-centered security workflow. |
| Behavior change depth | Medium — more targeted than traditional awareness tooling, but still closer to awareness-first design than full HRM. |
| Reporting & operational value | Best when paired with Mimecast email tooling and existing workflows. |
| Best for | Organizations already invested in Mimecast that want a more risk-aware awareness program. |
| What to validate | Whether the platform gives you enough depth in user-level modeling and continuous behavior change if HRM is the strategic goal. |
| Category fit | Emerging HRM / engagement-led awareness platform — stronger on adoption and storytelling than deep behavioral modeling. |
| Core strength | Story-driven security training that helps improve participation and retention. |
| Behavior change depth | Medium — strong for engagement, lighter on continuous risk scoring and adaptive response. |
| Reporting & operational value | Useful for awareness program owners tracking participation and culture change. |
| Best for | Teams prioritizing engagement, storytelling, and awareness adoption across broad user groups. |
| What to validate | Whether engagement gains translate into the level of measurable behavioral risk reduction your security team needs. |
| Category fit | Awareness-led / HRM-adjacent — widely used for security awareness and phishing simulation at scale. |
| Core strength | Large training library, broad coverage, and mature awareness program scaffolding. |
| Behavior change depth | Medium-Low — strong on campaigns and content breadth, lighter on individualized continuous adaptation. |
| Reporting & operational value | Well suited to awareness administration, compliance reporting, and large-scale rollout. |
| Best for | Organizations that need scale, breadth, and a familiar awareness platform model. |
| What to validate | Whether the platform can demonstrate continuous behavior change and user-level risk reduction rather than strong training coverage alone. |
| Category fit | Awareness-led / HRM-adjacent — strongest where phishing defense and email security alignment are top priorities. |
| Core strength | Threat-informed phishing simulations and close alignment with email security workflows. |
| Behavior change depth | Medium-Low — strong for phishing-focused defense, less broad in cross-channel human behavior management. |
| Reporting & operational value | Works best for teams already invested in Proofpoint’s email-centric security stack. |
| Best for | Organizations that want to align awareness closely to email threat patterns and phishing defense. |
| What to validate | Whether email-centric strength is enough if your goal is broader HRM across reporting behavior, segmentation, and continuous human risk reduction. |
How to evaluate human risk management platforms
Once you have a shortlist, the job changes.
You are no longer asking, “Which vendors are in this category?”
You are asking, “Which platform can actually reduce human risk in our environment?”
That requires a more disciplined evaluation framework because many platforms can demo well, but far fewer can support a mature, measurable HRM program after rollout.
1. Can the platform measure human risk at the user level?
This is the first filter and often the most revealing one.
A true human risk management platform should help you understand:
- Which users are high-risk
- Which teams or roles create more exposure
- How behavior changes over time
- Where interventions are working, stalling, or failing
If the platform mainly reports on completion rates, click rates and campaign summaries it may still be useful, but it is likely operating closer to awareness training than full HRM.
What to look for:
- Individual and group-level risk scoring
- Behavioral trend analysis over time
- Visibility by role, business unit, or risk segment
- Clear distinction between activity metrics and risk metrics
2. Does it adapt interventions or just schedule them?
This is one of the clearest differences between awareness-first tools and behavior-first platforms.
Many tools can deliver phishing campaigns, training modules, reminders and standard follow-up content.
But fewer can adapt based on things like user skill, reporting behavior and changing threat patterns. A strong HRM platform should not treat every user the same.
What to look for:
- Adaptive phishing difficulty
- Personalized learning paths
- Behavior-triggered micro-training
- Interventions that change based on improvement or decline
3. Can it prove measurable behavior change?
This is where many buying processes become vague and where the strongest teams get sharper.
You should be able to answer:
- Are users making better decisions over time?
- Are reporting behaviors improving?
- Are repeat-risk users improving faster?
- Is the organization becoming more resilient in ways leadership can understand?
The key is not just whether the platform generates data. It is whether that data supports a credible risk reduction story.
What to look for:
- Time-based improvement reporting
- Repeat-user behavior tracking
- Evidence of reduced exposure or stronger reporting outcomes
- Executive-ready metrics tied to business risk, not just training activity
4. How strong is the platform’s reporting and threat response workflow?
Human Risk Management should not live in a silo. The most valuable platforms connect human behavior to operational security workflows, especially around threat reporting, triage and escalation.
This matters because the best HRM programs do more than teach users to avoid mistakes. They help users become a more reliable part of detection and response.
What to look for:
- Built-in or integrated threat reporting workflows
- Fast feedback to users after actions are taken
- Clear reporting dashboards for admins and leadership
- Ability to operationalize human-generated signals
5. Does it fit your security operating model?
A platform can be strong in theory and still be the wrong fit in practice.
Some teams need low admin overhead and straightforward awareness coverage. Others need deep analytics, SOC alignment and more advanced segmentation.
The right platform depends on how your team actually operates, not just what looks strongest in a demo.
What to pressure-test:
- Admin effort after rollout
- Ease of configuration and maintenance
- Fit with your security team’s maturity
- Whether the platform supports the workflows you already rely on
6. How well does it integrate with your stack?
Integration matters because human risk does not exist in isolation.
The more mature the program, the more useful it becomes when it can connect to:
- Email environments
- Identity systems
- Reporting channels
- Security operations workflows
- Existing awareness or compliance programs
A platform that cannot share context or fit into the rest of your environment may create more friction than value.
What to look for:
- Email platform compatibility
- Identity and directory integration
- Reporting workflow support
- API access or integration flexibility
- Alignment with broader security tooling
7. Is the platform optimizing for awareness, analytics, or behavior change?
This question sounds simple, but it clarifies almost everything.
Most vendors tilt toward one of three models:
| Evaluation lens | What it prioritizes | Best fit for |
|---|---|---|
| Awareness-led | Training coverage, content libraries, compliance reporting, and phishing simulation campaigns. | Organizations needing scalable awareness programs, regulatory compliance coverage, and broad user education. |
| Analytics-led | Human risk scoring, behavioral analytics, segmentation, and visibility into user-level risk patterns. | Security teams focused on identifying high-risk users, prioritizing interventions, and improving risk visibility. |
| Behavior-change-led | Adaptive interventions, continuous learning, real threat reporting, and measurable behavior improvement over time. | Organizations aiming for measurable human risk reduction and integrating human behavior into security operations. |
This is often the most useful internal alignment question of the whole evaluation process.
Because once you know what outcome you want, the shortlist usually becomes much clearer.
A practical buyer checklist
Use these questions during demos, trials, or RFPs:
- Can you show user-level risk scoring, not just campaign results?
- How does the platform adapt for users who improve - or don’t?
- What evidence can you provide of behavior change over time?
- How does the platform support real threat reporting, not just simulations?
- What integrations matter most to get full value from the platform?
- How much ongoing admin work is required after launch?
- What does success look like after 6 or 12 months?
If a vendor answers these clearly, you are likely looking at a serious HRM contender.
Which human risk management platform Is right for your use case?
Most human risk management platforms are optimized for a specific outcome like phishing resilience, awareness, or analytics. Only a small number are designed to reduce human risk continuously across the organization.
The strategic difference most buyers miss
Most platforms in this space are optimized for a single layer:
- Phishing tools → detection of one attack vector
- Awareness platforms → content delivery at scale
- Analytics tools → visibility into risk
But human risk does not exist in layers, It;s continuous. The platforms that perform best long-term are the ones that combine measurement, intervention, and real-world behavior into a single system. This is where the gap between HRM as a feature and HRM as an operating model becomes visible.
| Use case | Primary goal | Best-fit vendors | Strategic limitation |
|---|---|---|---|
| Phishing resilience | Reduce clicks quickly | Proofpoint, KnowBe4 | Plateaus without broader behavior modeling |
| Risk visibility | Understand human risk | CybSafe | Requires additional execution layers |
| Engagement & culture | Improve participation | NINJIO | Limited measurable risk reduction |
| Ecosystem extension | Enhance existing stack | Mimecast Engage | Constrained to ecosystem scope |
| Full HRM maturity | Reduce human risk continuously | Hoxhunt | Requires strategic alignment (but highest upside) |
Sources
Hoxhunt Reviews (G2, Gartner, TrustRadius, Capterra, Software Advice)
CybSafe Reviews (Gartner Peer Insights, FeaturedCustomers)
KnowBe4 Reviews (Gartner, G2, FeaturedCustomers)
Proofpoint Reviews (Gartner, G2, Capterra)
Mimecast Engage Reviews (Gartner, G2, TrustRadius)
- Subscribe to All Things Human Risk to get a monthly round up of our latest content
- Request a demo for a customized walkthrough of Hoxhunt







